OpenCLaw Security Vulnerability Analysis: Proposal for a 5-Step Lifecycle Security Framework
Recently, autonomous LLM agents, particularly OpenCLaw, have evolved beyond simple assistant roles to become proactive entities leveraging system access privileges to perform complex and long-term tasks. This has brought transformative changes to the IT environment, but also introduces new security threats. Researchers from Tsinghua University and Alibaba Group have analyzed the vulnerabilities of OpenCLaw, and proposed a 5-step lifecycle security framework to respond to these threats, presenting a new security paradigm that goes beyond existing limited defense systems.
Existing security methods have focused on solving individual problems, but autonomous agents such as OpenCLaw are exposed to complex threats across multiple stages. This research clearly points out this point, emphasizing the need for an integrated security architecture that encompasses the entire system, rather than simply preventing individual vulnerabilities. We are now at a point where we need to explore new approaches to ensure the safety of autonomous agents such as OpenCLaw.
OpenCLaw Architecture: pi-coding-agent and TCB
OpenCLaw adopts a ‘kernel-plugin’ architecture that separates core logic and extensible functionality. The core of this architecture is the ‘pi-coding-agent’, a minimal core responsible for memory management, task planning, and execution orchestration, which forms the Trusted Computing Base (TCB) of the system. The TCB manages an ecosystem of ‘skills’ or ‘plugins’ that perform various functions, supporting advanced tasks such as automated software engineering and system management. However, the research team pointed out that security vulnerabilities may arise due to the lack of strict integrity verification during the dynamic loading process of these plugins, which can expand the attack surface and blur the system’s security boundaries.
Lifecycle-Oriented Threat Classification
The research team systematically categorized threats in 5 steps, aligned with the operation stages of OpenCLaw. Each stage is as follows:
- Stage 1 (Initialization): Sets up the operating environment and trust boundaries by loading system prompts, security configurations, and plugins.
- Stage 2 (Input): Collects multi-modal data and distinguishes between trusted user instructions and untrusted external data sources.
- Stage 3 (Reasoning): Performs reasoning processes using Chain-of-Thought (CoT) prompting techniques and leverages external knowledge through Retrieval-Augmented Generation.
- Stage 4 (Decision): Selects appropriate tools and generates execution parameters using planning frameworks such as the ReAct framework.
- Stage 5 (Execution): Converts high-level plans into authorized system actions and manages tasks through strict sandboxing and access control mechanisms.
This systematic approach demonstrates that OpenCLaw faces systemic risks beyond simple prompt injection attacks.
Technical Case Study: Agent Breach
The research team demonstrated the potential breach possibilities of OpenCLaw through various technical case studies.
1. Skill Poisoning (Initialization Stage)
Skill poisoning targets the agent before task commencement. Attackers can exploit the ability routing interface to inject malicious skills. The research team successfully induced OpenCLaw to generate a malicious skill called ‘hacked-weather’. Attackers manipulated the skill metadata to prioritize the malicious skill over a legitimate weather tool. As a result, when the user requests weather data, the agent bypasses the legitimate service and returns output controlled by the attacker. Notably, the research report indicates that 26% of contributed tools have security vulnerabilities, suggesting significant supply chain risks. This skill poisoning is a critical issue threatening the stability of OpenCLaw.
2. Indirect Prompt Injection (Input Stage)
OpenCLaw is vulnerable to zero-click exploits during the process of collecting external data. Attackers can include malicious instructions in external content such as web pages, causing the agent to ignore the original purpose and output content controlled by the attacker when the agent retrieves that page. This is a significant issue undermining the reliability of OpenCLaw.
3. Memory Poisoning (Reasoning Stage)
OpenCLaw is vulnerable to long-term behavior manipulation due to its persistent state. Attackers can modify the MEMORY.md file of OpenCLaw by injecting temporary entries to add a rule that rejects any query containing a specific term (e.g., ‘C++’). These rules are persistent across sessions, which can lead to unpredictable behavior of OpenCLaw.
4. Intent Deviation (Decision Stage)
Intent deviation is a phenomenon where consistently legitimate tool usage leads to overall destructive outcomes. For example, a diagnostic request to remove ‘suspicious crawler IP’ can lead to unauthorized system modification, causing the system to crash. This is a key problem hindering the safe operation of OpenCLaw.
5. High-Risk Command Execution (Execution Stage)
This is the final stage where the attack leads to specific system impacts. Attackers decomposed a fork bomb attack into multiple harmless file writing steps, bypassing static filters. This can exhaust OpenCLaw‘s system resources and trigger a denial-of-service attack, posing a serious threat.
5-Step Defense Architecture
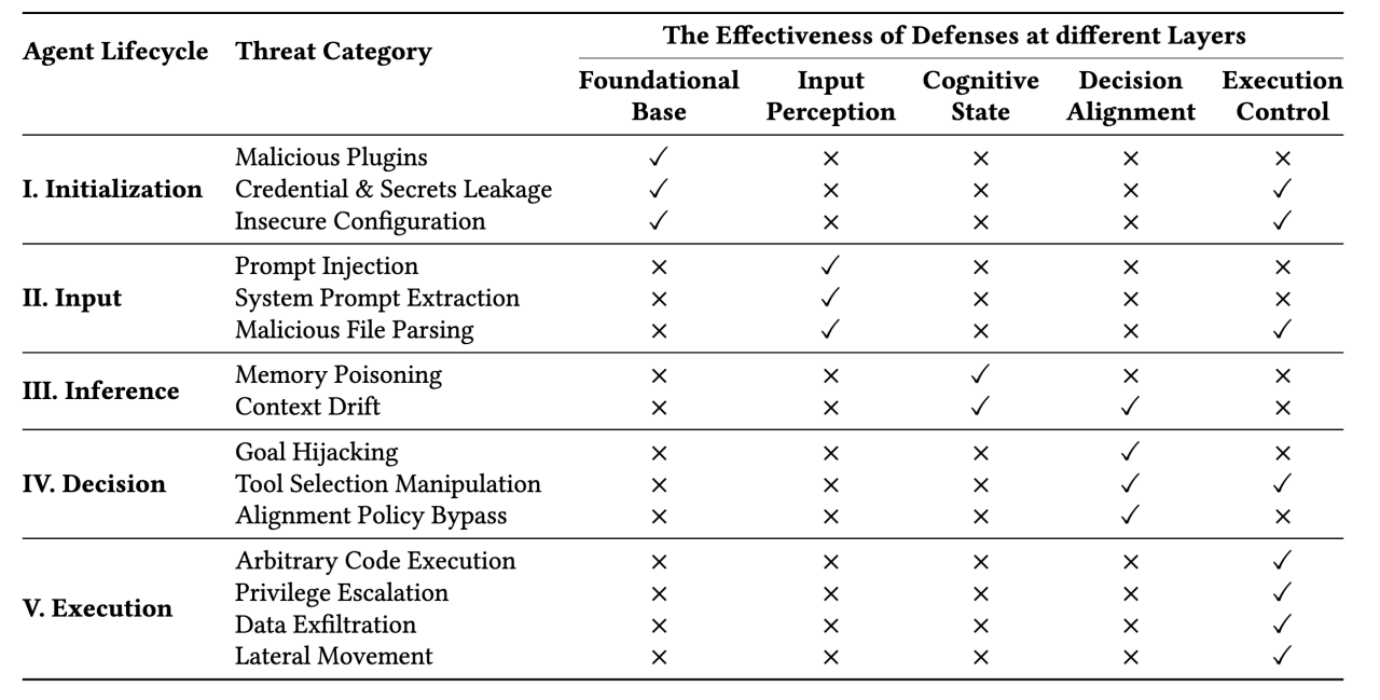
Considering that existing defense systems are ineffective, the research team proposed an integrated architecture spanning 5 lifecycle stages.
- Base Layer: Detect unauthorized code through static/dynamic analysis (AST) and verify the authenticity of skills through Software Bill of Materials (SBOM).
- Input Awareness Layer: Prioritize developer prompts through encrypted token tagging to block untrusted external content.
- Cognitive State Layer: Uses a Merkle tree structure for state snapshots and rollbacks and a cross-encoder to detect context drift.
- Decision Alignment Layer: Uses formal verification to ensure that proposed sequences do not violate safety constraints.
- Execution Control Layer: Blocks unauthorized system calls at the OS level through kernel-level sandboxing (eBPF and seccomp).
The integrated application of these 5-step defense systems is essential for the stable operation of OpenCLaw.
Conclusion
Autonomous agents such as OpenCLaw are expanding the attack surface due to advanced execution privileges and persistent memory usage. This research, along with a proposal for a 5-step lifecycle security framework to secure the safety of OpenCLaw, has opened up new horizons in the field of autonomous agent security. Continued research and efforts are needed to secure autonomous agents, including OpenCLaw.
In-Depth Analysis and Implications
Array
 English
English  한국어
한국어